LXMF is a simple and flexible messaging format and delivery protocol that allows a wide variety of implementations, while using as little bandwidth as possible. It is built on top of Reticulum and offers zero-conf message routing, end-to-end encryption and Forward Secrecy, and can be transported over any kind of medium that Reticulum supports.
LXMF is efficient enough that it can deliver messages over extremely low-bandwidth systems such as packet radio or LoRa. Encrypted LXMF messages can also be encoded as QR-codes or text-based URIs, allowing completely analog paper message transport.
User-facing clients built on LXMF include:
LXMF messages are stored in a simple and efficient format, that's easy to parse and write.
In some cases the actual message-id cannot be inferred, for example when a Propagation Node is storing an encrypted message for an offline user. In theses cases a transient-id is used to identify the message while in storage or transit.
Destination, Source, Signature and Payload parts are mandatory, as is the Timestamp part of the payload.
The Content, Title and Fields parts must be included in the message structure, but can be left empty.
The Fields part can be left empty, or contain a dictionary of any structure or depth.
LXMF offers flexibility to implement many different messaging schemes, ranging from human communication to machine control and sensor monitoring. Here's a few examples:
A messaging system for passing short, simple messages between human users, akin to SMS can be implemented using only the Content field, and leaving all other optional fields empty.
For sending full-size mail, an email-like system can be implemented using the Title and Content fields to store "subject" and "body" parts of the message, and optionally the Fields part can be used to store attachments or other metadata.
Machine-control messages or sensor readings can be implemented using command structures embedded in the Fields dictionary.
Distributed discussion or news-groups, akin to USENET or similar systems, can be implemented using the relevant fields and LXMF Propagation Nodes. Broadcast bulletins can be implemented in a similar fashion.
LXM Propagation Nodes offer a way to store and forward messages to users or endpoints that are not directly reachable at the time of message emission. Propagation Nodes can also provide infrastructure for distributed bulletin, news or discussion boards.
When Propagation Nodes exist on a Reticulum network, they will by default peer with each other and synchronise messages, automatically creating an encrypted, distributed message store. Users and other endpoints can retrieve messages destined for them from any available Propagation Nodes on the network.
The LXM Router handles transporting messages over a Reticulum network, managing delivery receipts, outbound and inbound queues, and is the point of API interaction for client programs. The LXM Router also implements functionality for acting as an LXMF Propagation Node.
Programatically, using the LXM Router to send a message is as simple as:
import LXMF
lxm_router = LXMF.LXMRouter()
message = LXMF.LXMessage(destination, source, "This is a short, simple message.")
lxm_router.handle_outbound(message)
The LXM Router then handles the heavy lifting, such as message packing, encryption, delivery confirmation, path lookup, routing, retries and failure notifications.
LXMF uses encryption provided by Reticulum, and thus uses end-to-end encryption by default. The delivery method of a message will influence which transport encryption scheme is used.
A message can be delivered opportunistically, embedded in a single Reticulum packet. In this cases the message will be opportunistically routed through the network, and will be encrypted with ephemeral keys derived with ECDH on Curve25519. This mode offers Perfect Forward Secrecy.
If a message is delivered to the Reticulum GROUP destination type, the message will be transported using AES-128 encryption.
If a message is delivered over a Reticulum link (which is the default method), the message will be encrypted with ephemeral keys derived with ECDH on Curve25519. This mode offers Perfect Forward Secrecy.
Assuming the default Reticulum configuration, the binary wire-format is as follows:
The complete message overhead for LXMF is only 99 bytes, which in return gives you timestamped, digitally signed, infinitely extensible, end-to-end encrypted, zero-conf routed, minimal-infrastructure messaging that's easy to use and build applications with.
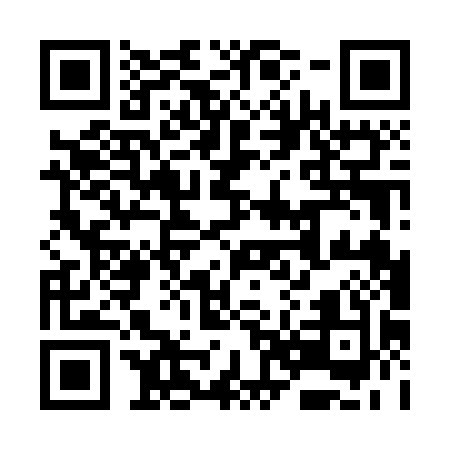
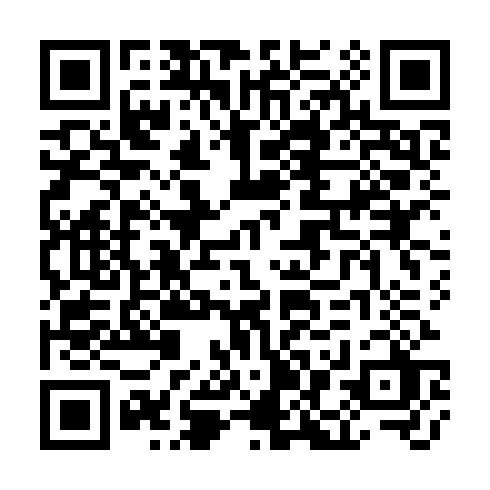
You can try out the paper messaging functionality by using the following QR-code. It is a paper message sent to the LXMF address 6b3362bd2c1dbf87b66a85f79a8d8c75. To be able to decrypt and read the message, you will need to import the following Reticulum Identity to an LXMF messaging app:
3BPTDTQCRZPKJT3TXAJCMQFMOYWIM3OCLKPWMG4HCF2T4CH3YZHVNHNRDU6QAZWV2KBHMWBNT2C62TQEVC5GLFM4MN25VLZFSK3ADRQ=
The Sideband application allows you to do this easily. After the you have imported the identity into an app of your choice, you can scan the following QR-code and open it in the app, where it will be decrypted and added as a message.

You can also find the entire message in this link:
lxm://azNivSwdv4e2aoX3mo2MdTAozuI7BlzrLlHULmnVgpz3dNT9CMPVwgywzCJP8FVogj5j_kU7j7ywuvBNcr45kRTrd19c3iHenmnSDe4VEd6FuGsAiT0Khzl7T81YZHPTDhRNp0FdhDE9AJ7uphw7zKMyqhHHxOxqrYeBeKF66gpPxDceqjsOApvsSwggjcuHBx9OxOBy05XmnJxA1unCKgvNfOFYc1T47luxoY3c0dLOJnJPwZuFRytx2TXlQNZzOJ28yTEygIfkDqEO9mZi5lgev7XZJ0DvgioQxMIyoCm7lBUzfq66zW3SQj6vHHph7bhr36dLOCFgk4fZA6yia2MlTT9KV66Tn2l8mPNDlvuSAJhwDA_xx2PN9zKadCjo9sItkAp8r-Ss1CzoUWZUAyT1oDw7ly6RrzGBG-e3eM3CL6u1juIeFiHby7_3cON-6VTUuk4xR5nwKlFTu5vsYMVXe5H3VahiDSS4Q1aqX7I
On operating systems that allow for registering custom URI-handlers, you can click the link, and it will be decoded directly in your LXMF client. This works with Sideband on Android.
LXMF is beta software, and should be considered experimental. While it has been built with cryptography best-practices very foremost in mind, it has not been externally security audited, and there could very well be privacy-breaking bugs. If you want to help out, or help sponsor an audit, please do get in touch.
If you want to try out LXMF, you can install it with pip:
pip3 install lxmf
LXMF is actively being developed, and the following improvements and features are currently planned for implementation:
You can help support the continued development of open, free and private communications systems by donating via one of the following channels:
84FpY1QbxHcgdseePYNmhTHcrgMX4nFfBYtz2GKYToqHVVhJp8Eaw1Z1EedRnKD19b3B8NiLCGVxzKV17UMmmeEsCrPyA5w
0xFDabC71AC4c0C78C95aDDDe3B4FA19d6273c5E73
35G9uWVzrpJJibzUwpNUQGQNFzLirhrYAH
https://ko-fi.com/markqvist